Security threats in large organizations have been a big concern in recent years. Cybersecurity risks are no longer just an IT problem; they affect the entire business and can have serious financial and reputational consequences. Large organizations have a lot to lose, whether it’s a data breach, ransomware attack, or internal misuse of sensitive information. That’s where a cybersecurity risk assessment comes into play.
So, let’s dive into what a cybersecurity risk assessment is, why it’s important, and how you can perform one effectively in a large organization.
Cybersecurity risk assessment refers to a method of identifying, evaluating, and prioritizing cyber threats and vulnerabilities that may harm the organization, its information systems, and overall operations.
Put simply, it is like auditing all the doors and windows of a digital house, ensuring they are secure and identifying the ones most likely to be targeted by intruders.
You might be thinking, Why go through the hassle? Here’s why:
A real-world example is seen in Cybersecurity Solutions for healthcare, where assessments help safeguard patient data and meet HIPAA standards.
When done right, a cybersecurity risk assessment offers major wins:
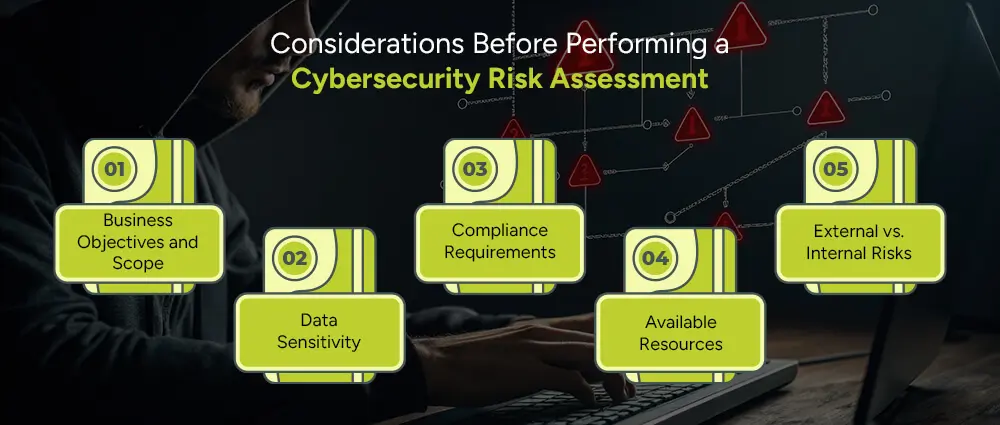
Before diving into a cybersecurity risk assessment, it’s important to pause and reflect on a few key things. This helps make sure your efforts are focused, effective, and aligned with your actual needs. Here are five important factors to think about:
Start by asking yourself: What are we trying to protect, and why?
Are you scanning the whole organization or just a particular part, like your finance department or customer service platform? A clear scope makes a great deal of difference. For example, if you wanted to protect customer data, your assessment would look something more like databases, CRM systems, and access control.
However, if you intended to examine your entire business, your approach would have had to encompass a larger spectrum by department, from HR to IT.
Think of it like planning a road trip; you need to know your destination before mapping the route.
Not all data is created equal. Some information is much more sensitive than others, and understanding the different kinds of data that exist in your organization is critical to every risk assessment. This becomes even more critical when undertaking initiatives like Big Data Migration, where large volumes of data shift between environments.
Ask yourself: Does your organization store customer credit card information? employee medical records, or confidential business strategies? Recognizing the sensitivity of each data type helps prioritize security measures and focus on the highest-risk areas.
The regulations or standards that will be applicable to your business will depend heavily on the industry. These are not optional; they are legal and operational requirements. For instance, healthcare organizations must comply with HIPAA, while financial firms may follow PCI-DSS or SOX standards.
Considering these regulations during a risk assessment helps avoid fines and protects stakeholder trust.
No organization has unlimited money, time, or manpower. It’s important to realistically evaluate the resources available.
Will the assessment be internal or outsourced? Are the right vulnerability scanning tools available? Your approach should reflect the resources available, whether for a high-level assessment or a detailed, technology-driven evaluation.
Cyber threats may be from anywhere, external or internal ones emanated by employee negligence, misuse of access, or even insider attacks. Both types of risks must be considered to build a complete picture of your cybersecurity landscape.
For example, do employees use strong passwords? Are access controls in place? Balancing internal and external risks ensures that no significant threat goes unnoticed.
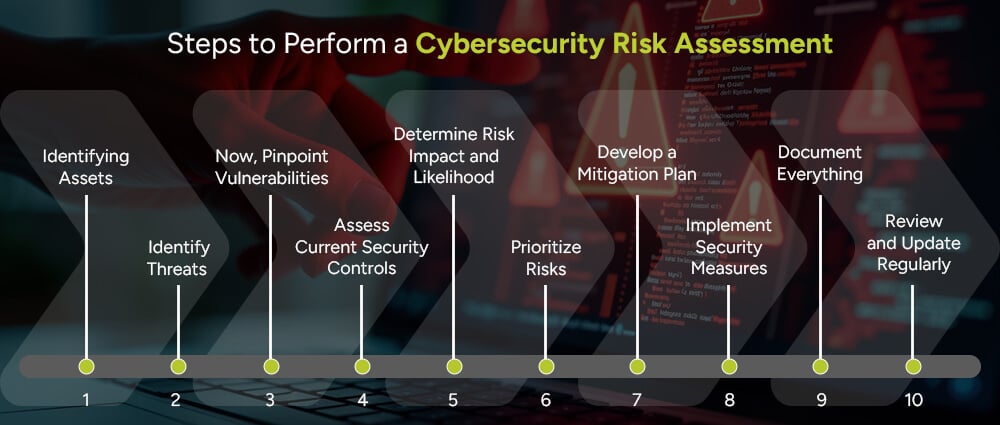
In large corporations, understanding your system environment and infrastructure risks is crucial. The following steps provide a structured approach to identifying, evaluating, and managing threats:
Start by listing all your critical assets. This includes computers, servers, mobile devices, software applications, and sensitive data. Think about everything that plays a role in your day-to-day operations.
You can’t protect what you don’t know exists, so be thorough and organized here.
Next, ask yourself: What could go wrong? Threats can spring out of nowhere, and could be anything from phishing emails and ransomware to natural disasters or insider mistakes. Don’t forget there’s always a risk of less-obvious threats, such as stolen devices or social engineering.
One tip to follow in this scenario is to get creative; it will help you stay ahead of any malicious intrusions.
Now, look for weak points that make your systems vulnerable. This could entail outdated software, weak passwords, or a lack of employee security training.
Any exploitable gap must be documented for mitigation.
Take stock of what protections you already have in place. firewalls, antivirus tools, access restrictions, etc.
Evaluate whether these controls are effective and up to date to help you identify any remaining gaps.
For each threat and vulnerability combo, consider how likely it is to occur and how bad the impact would be. Would it cause a minor inconvenience or bring your whole system down?
This allows you to rank your risks from “nice to fix” to “must fix now.”
Now that you know the biggest risks, it’s time to prioritize. Start with those that are both highly likely and highly damaging. This ensures that resources are allocated where they matter most.
For each top-priority risk, create a step-by-step plan to reduce or eliminate it. This might include applying software patches, strengthening policies, getting a good cybersecurity patch management team, or training staff. Think practical, actionable, and tailored to your specific setup.
Put your mitigation strategies into action. Whether that’s configuring a firewall or training your team, execution is key. It is your duty to ensure that each action is tracked and completed thoroughly.
Keep detailed records of your risk assessment process, what you found, what you fixed, and what’s still pending. Documentation is essential for audits, compliance, and continuous improvements. It’s also helpful for onboarding new team members or when reviewing past issues.
Remember, Cyber threats aren’t a one-time thing. So, neither should your risk assessment be a once-in-a-lifetime thing. Set a schedule to review and refresh your process. Ideally, every 6 to 12 months or after major changes.
Staying proactive keeps your defenses strong and relevant.
Organizations that have achieved success with big data often emphasize cybersecurity assessments as a crucial part of their digital transformation journey.
Let’s say your company stores customer data in a cloud system. A risk assessment in cybersecurity would look something like this:
No organization is immune to cyber threats. However, with a structured cybersecurity risk assessment process, you can stay several steps ahead of attackers. Whether you’re a large enterprise or a small startup, performing regular assessments is one of the smartest ways to secure your digital future.
Consider using trusted risk assessment services to guide you through the process and customize it to your needs.
A cybersecurity risk assessment checklist is a step-by-step guide that helps ensure all critical elements of the risk assessment process are covered. It typically includes:
Large organizations handle vast amounts of data, use complex systems, and have multiple entry points for attacks. A cyber risk assessment ensures they stay ahead of potential threats, avoid costly breaches, maintain trust, and meet compliance requirements.
Absolutely. Small businesses are often prime targets for cybercriminals because they may lack strong security controls. A basic risk assessment cybersecurity checklist can help small businesses protect sensitive data, stay compliant, and reduce the chances of cyberattacks, without breaking the bank.