In today’s fast-moving digital world, the old ways of securing applications and infrastructure are being left behind. Chief Technology Officers (CTOs) in the United States and around the globe are rethinking how they defend their systems. Continuous penetration testing services are emerging as a modern alternative to traditional annual testing.
In this guide, we will explore:
If this sounds like something you want to learn, then continue on:
For many companies, especially in regulated industries, annual penetration testing is a checkbox. A penetration testing company conducts an engagement once a year. Then, the systems go untested for the next 364 days. This creates a dangerous gap.
Annual tests were once the norm because they fit auditing cycles. But the threat environment has changed. New vulnerabilities appear daily. Software updates change systems hourly. Business risk evolves rapidly. In this context, annual testing is outdated.
Imagine this: a company undergoes a detailed vulnerability assessment and penetration testing (VAPT) engagement in January. A new critical vulnerability appears in March. A breach happens in June. The next scheduled test is scheduled for December.
That is more than 250 days where threats can move undetected. This long vulnerability window is a key reason CTOs are exploring continuous penetration testing services.
The problem is simple:
In many data breaches, hackers don’t wait around for months to take advantage of a weakness. Research shows that once a vulnerability is made public, attackers often strike within just a few days.
On average, it takes about five days for a newly disclosed vulnerability to be exploited in the real world. This means that by the time most organizations detect the issue and apply a fix, attackers may have already taken advantage of it.
A clear example of this is the Equifax breach. Hackers took advantage of a known flaw in the Apache Struts software. Even though a patch or patch management to fix the issue had been available for months, Equifax didn’t install it in time. As a result, attackers exploited this vulnerability and were able to access the personal information of hundreds of millions of people.
High-profile breaches, especially in the US, often show the same pattern:
The cost of a breach can be devastating:
According to industry data, delayed detection can cost companies millions. A faster vulnerability identification strategy isn’t just a good security practice. It’s a business imperative.
Let’s define what CTOs are now prioritizing.
Continuous penetration testing services are an ongoing process of testing systems for weaknesses on a regular and automated basis. Instead of a once-a-year snapshot, continuous testing works like a security radar. It constantly hunts for vulnerabilities across systems, networks, cloud resources, web applications, APIs, and more.
The core principles include:
This model adapts to change and gives security teams ongoing visibility into vulnerabilities.
The differences are substantial:
| Feature | Annual Pen Testing | Continuous Pen Testing |
| Frequency | Once or twice a year | Constant |
| Coverage | Snapshot in time | Ongoing scanning + attack simulation |
| Detection Time | Months | Hours or days |
| Adaptability | Limited | Adjusts to changes automatically |
| Integration | Standalone report | Integrated with DevSecOps |
| Cost Efficiency | Expensive on demand | Better ROI over time |
Annual testing is manual, scheduled, and static. Continuous automated penetration testing is dynamic, automated, and real-time.
At the heart of continuous testing is technology. Platforms that support continuous automated penetration and attack testing combine several tools and techniques:
Rather than waiting for humans to schedule tests, these tools run continuously, prioritizing and validating findings automatically.
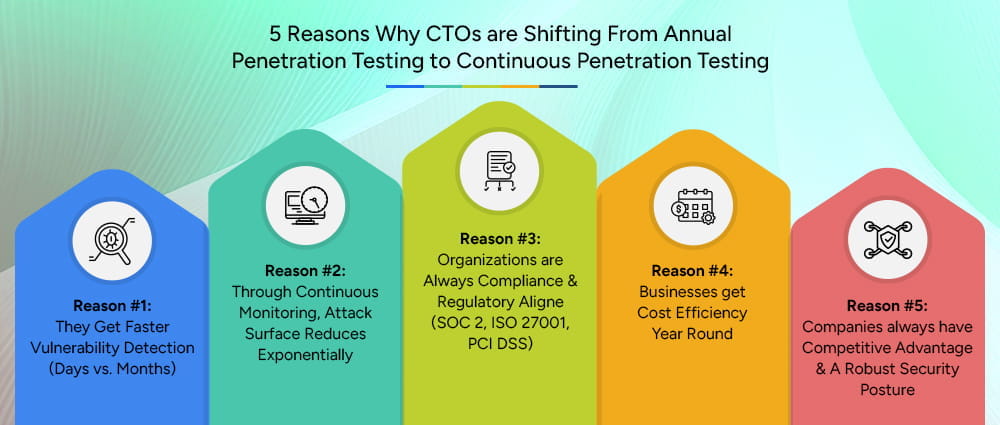
CTOs are investing in continuous testing for strategic business reasons. Below are five major drivers of this shift.
Traditional annual tests might miss vulnerabilities that emerge between engagements. Continuous testing finds issues as soon as they appear. Faster detection reduces risk and prevents attackers from having a long window to exploit weaknesses.
This is especially important for organizations that push code frequently, scale infrastructure dynamically, or operate in competitive markets.
Modern environments are highly dynamic. New assets appear overnight. Web application penetration testing once a year does not discover new APIs, new cloud configurations, or changes in microservices.
Continuous penetration testing services monitor the full attack surface all the time, mapping new assets and checking for vulnerabilities. This reduces the threat surface and keeps defenses proactive.
Many compliance frameworks require regular testing. But auditors now expect more than yearly snapshots.
Continuous testing helps organizations:
This approach aligns with frameworks like:
Continuous testing is transforming compliance from a checkbox into an ongoing activity.
While annual tests may be cheaper in one engagement, their limited value adds up. Fixing vulnerabilities late costs more. Emergency incident response is expensive.
Continuous testing spreads the cost over time. Teams fix issues early. Automation reduces manual labor. The result is a better return on security investment.
In the United States, companies that can prove robust security enjoy trust advantages in the market. Continuous testing:
Customers and partners increasingly demand solid security practices. Continuous approaches deliver demonstrable assurance.
Let’s dive deeper into how these approaches compare.
Annual: Lump sum engagements
Continuous: Subscription or platform-based cost over time
Continuous testing provides more value for money by catching issues early.
Annual: Requires scheduling and coordination with external testers
Continuous: Managed through automation and integrated tooling
Annual: Meets minimum audit requirements
Continuous: Supports ongoing compliance and risk posture improvement
Understanding the mechanics helps CTOs and security leaders evaluate solutions.
Continuous platforms run automated scanning regularly. They detect new vulnerabilities immediately. They also prioritize findings based on risk, business impact, and exploitability.
Assets change. Servers, containers, APIs, and cloud services get added. Automated mapping keeps track of all assets, ensuring nothing is missed.
Modern systems simulate attack behaviors using artificial intelligence. This goes beyond scanning. It tests whether vulnerabilities can be exploited, replicating real-world attacker tactics.
Security teams get alerts and dashboards that show vulnerabilities in context. They see trends, urgent risks, and remediation guidance. This helps teams act faster and with clarity.
A big question is: which vendor or provider should you choose? Here’s how to evaluate.
When selecting continuous penetration testing providers, consider:
Ask potential providers about:
A key success factor is how well continuous testing integrates with existing tools:
When speaking with penetration testing companies that offer continuous services:
Asking these questions helps identify the right fit.

Transitioning to continuous penetration testing services is a structured journey. Each phase builds on the previous one, helping organizations move from occasional testing to a living, ongoing security practice without disrupting operations.
Measuring results is essential to prove the value of continuous testing to leadership and stakeholders.
MTTD shows how quickly vulnerabilities are discovered after they appear. With continuous testing, this time should drop from months to days or even hours.
This metric tracks how fast teams fix identified issues. A higher remediation rate indicates strong coordination between detection and response.
Over time, your overall risk rating should decrease. Continuous testing steadily removes high-risk vulnerabilities from the environment.
This shows the financial efficiency of your security strategy. Continuous testing often reduces this cost by detecting issues early before they escalate.
Improved audit outcomes demonstrate the effectiveness of your approach. Continuous testing provides consistent evidence for SOC 2, ISO 27001, and PCI DSS audits.
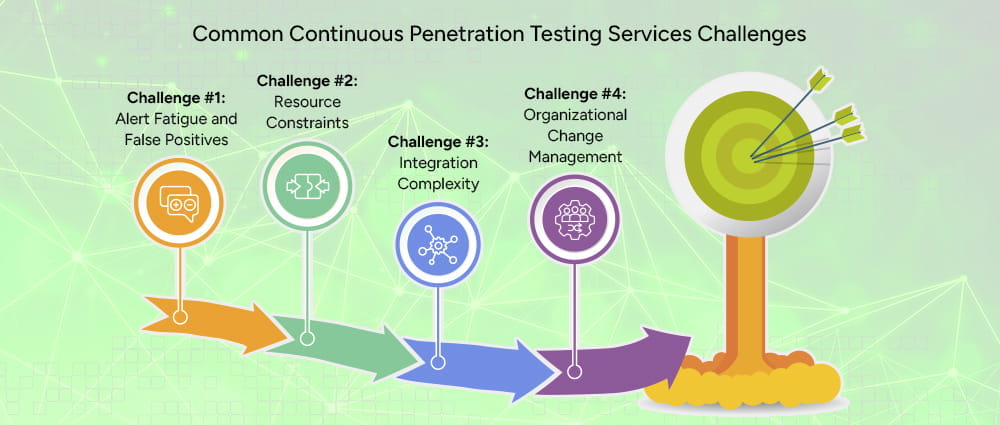
Adopting continuous testing is powerful but not without challenges. Understanding them early helps ensure smooth adoption.
When testing runs continuously, alerts can quickly pile up. Security teams may start ignoring notifications because they cannot tell which issues truly matter. This is especially common when tools generate false positives or low-risk findings that distract from real threats.
To overcome this, organizations should rely on platforms that offer risk-based prioritization and intelligent filtering. Custom alert thresholds, severity scoring, and validation mechanisms help teams focus only on exploitable, high-impact vulnerabilities instead of chasing noise.
Many security and IT teams are already stretched thin. Introducing continuous penetration testing services may feel like adding more work to an already full plate. Without proper workflows, teams may struggle to keep up with the steady stream of findings.
The solution lies in automation and integration. When findings automatically create tickets in existing systems and align with DevOps processes, remediation becomes part of daily work rather than an extra burden. This reduces manual effort and makes continuous testing sustainable even for smaller teams.
Continuous testing platforms need to connect with SIEM tools, CI/CD pipelines, cloud platforms, ticketing systems, and monitoring dashboards. Without careful planning, this integration can become technically complex and delay adoption.
Early involvement of DevOps, IT, and security teams is essential. Choosing tools that offer native integrations and clear documentation also simplifies deployment. A phased rollout, starting with a pilot environment, allows teams to solve integration issues before full implementation.
The shift from annual penetration testing to continuous monitoring is not just technical. It is cultural. Teams are used to treating penetration testing as a once-a-year event rather than an ongoing responsibility.
Leadership must communicate why this change matters and how it improves the overall security posture. Training sessions, clear workflows, and shared accountability across teams help build a culture where continuous testing is seen as a normal part of operations rather than an additional task.
Understanding these challenges in depth helps teams prepare realistic solutions instead of becoming overwhelmed by the transition.
The future of vulnerability assessment and penetration testing will require ongoing development work. Organizations now utilize continuous penetration testing services which operate using artificial intelligence to deliver faster results with deeper testing capabilities.
Organizations can achieve security breach prevention through their automated workflows which enable them to identify threats before they occur.
Companies that implement continuous testing in today’s fast-changing digital world will achieve both improved security measures and enhanced competitive advantage. Organizations use Arpatech’s Governance, Risk, and Compliance advisory services to support their transformation process.
Arpatech provides security leaders and chief technology officers with expert guidance and continuous penetration testing automation insights to assist their decision-making processes by:
With Arpatech’s approach, organizations don’t just implement tools; they embed continuous penetration testing services into a broader GRC strategy, ensuring that risk management, regulatory alignment, and cybersecurity work together seamlessly. This approach allows leadership teams to make informed decisions with confidence while maintaining resilience against evolving threats.
Let’s protect your next Project together.
Continuous automated penetration testing is a method of checking your systems for security weaknesses on an ongoing basis.
Unlike traditional annual tests, this approach runs automatically and continuously, scanning networks, applications, and endpoints to identify vulnerabilities as soon as they appear.
This helps organizations stay ahead of attackers by finding and fixing issues quickly, instead of waiting months between tests.
Continuous penetration testing is designed to run constantly. Some organizations schedule daily scans, while others use real-time monitoring that checks for vulnerabilities as systems change or new code is deployed.
The goal is to catch problems as soon as they appear so teams can act quickly, reducing the window of opportunity for attackers.
Continuous testing focuses on automated, ongoing scanning to detect vulnerabilities regularly. Red teaming, on the other hand, is a manual approach where security experts simulate real-world attacks to see if systems can be breached.
Continuous testing finds issues early and repeatedly, while red teaming tests defenses in realistic attack scenarios. Both are valuable, but they serve different purposes.
The cost depends on the size of your environment, the number of systems, and the level of automation you need.
While it may seem like a larger upfront investment than annual tests, continuous penetration testing often saves money over time by preventing breaches, reducing downtime, and improving compliance.
Organizations usually find it more cost-effective when considering the potential damage from delayed vulnerability detection.
The best providers offer automated testing, real-time reporting, and seamless integration with your existing security tools. They should be able to cover web applications, networks, and cloud systems while providing clear guidance on remediation.
Look for providers with a strong track record, solid customer support, and the ability to align with compliance frameworks like SOC 2, ISO 27001, or PCI DSS.
You can justify the investment by showing how continuous penetration testing reduces risk, speeds up detection, and improves overall security. It also helps with regulatory compliance and provides evidence for audits.
Leadership can see the value in preventing costly breaches, avoiding downtime, and protecting sensitive data, making the cost of continuous testing far less than the potential cost of an incident.