Security budgets are tighter than ever, threats are more sophisticated than they’ve ever been, and the C-suite is asking harder questions than ever before. If you’re a CTO, CISO, or security leader trying to figure out how to best protect your organization, you’ve probably heard the terms “red teaming” and “penetration testing” used almost interchangeably.
They’re not the same thing. And choosing the wrong one could leave your organization dangerously exposed, or burn tens of thousands of dollars on an assessment that doesn’t actually answer your most urgent questions.
Today, we’ll break down both approaches, red teaming vs pen testing, and help you understand what each assessment does, when you need it, and how to make the right call for your organization’s specific situation.
The confusion is understandable. Both involve skilled security professionals attempting to breach your defenses. Both produce reports with findings and recommendations. Both are marketed by vendors with similar-sounding promises. The overlap in terminology doesn’t help either, vendors sometimes call basic penetration tests “red team assessments” to make them sound more comprehensive than they actually are.
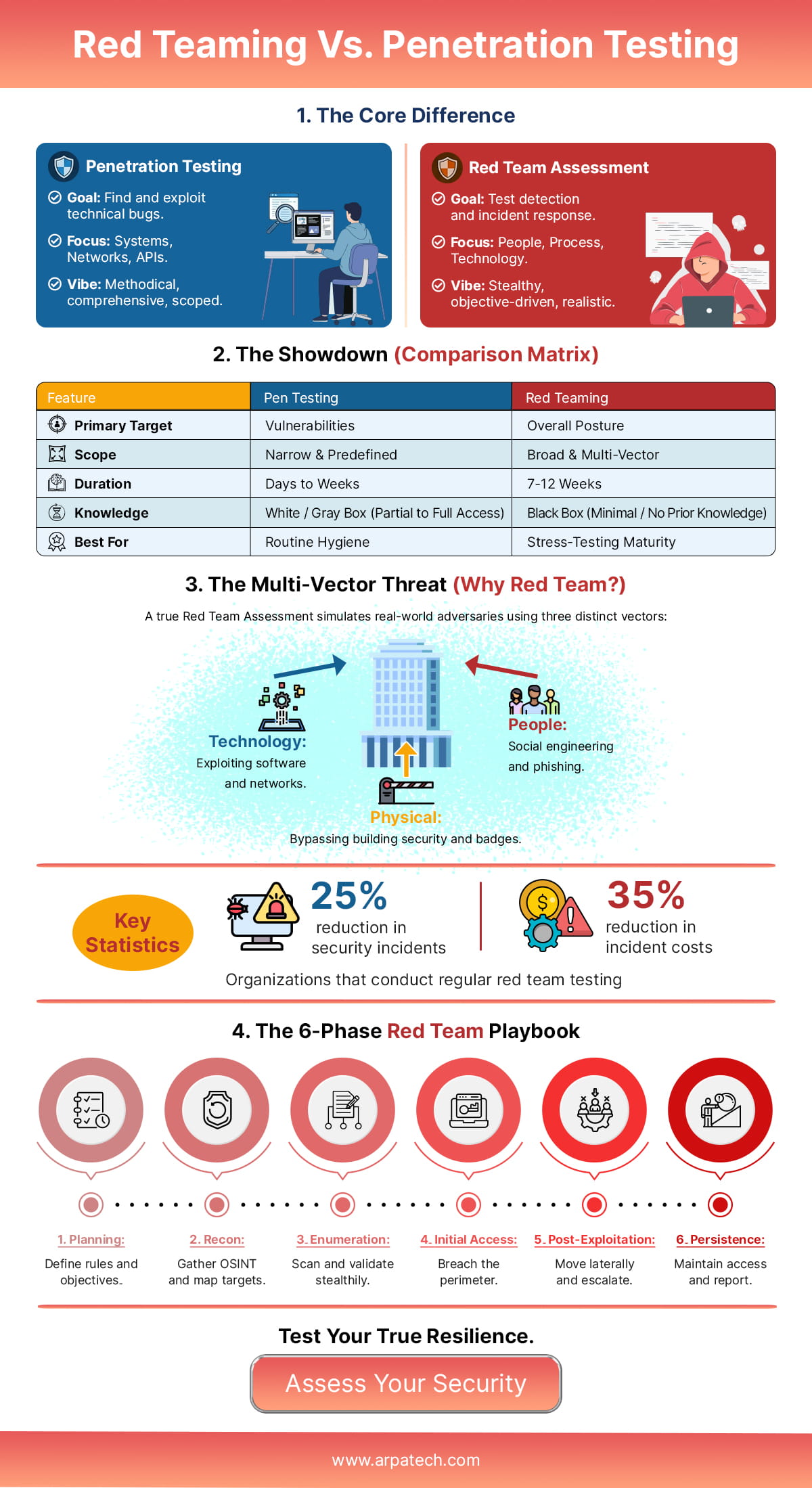
The deeper issue is that both approaches are genuinely valuable, but they answer different questions entirely. Penetration testing asks: “Are these specific systems vulnerable?” Red teaming asks: “Could a real attacker achieve a meaningful business objective inside our environment?” These are fundamentally different questions, and the methodologies used to answer them are worlds apart.
Selecting the wrong assessment type isn’t just an academic problem. Organizations that run a penetration test when they actually need red teaming often walk away with a false sense of security. They patch a list of CVEs, close some open ports, and assume they’re protected, not realizing that a sophisticated attacker doesn’t need a single critical vulnerability to cause catastrophic damage. They chain together low-severity issues, leverage social engineering, and move laterally through an environment using legitimate credentials and tools.
On the other side, organizations that jump straight to red teaming before their security fundamentals are solid waste money. If you have exploitable, unpatched systems across your network, a full red team engagement will find those fast and stop there; you didn’t need a $150,000 engagement to tell you to patch your systems. A well-scoped penetration test would have been far more cost-effective and actionable.
A red team assessment is a comprehensive, adversary-simulation exercise in which a specialized team of security professionals attempts to compromise an organization’s defenses using the same tactics, techniques, and procedures (TTPs) that real-world threat actors use. The goal of red teaming is not simply to find vulnerabilities; it’s to answer one critical question: “Can a realistic attacker achieve a meaningful objective inside our organization?”
That objective might be exfiltrating customer data, accessing the CEO’s email, disrupting manufacturing systems, or pivoting from a compromised workstation to domain administrator access. Red teaming is as much about testing people and processes as it is about testing technology.
Unlike a penetration test, which typically has a clearly defined, limited scope, a red team security assessment is intentionally broad and mission-focused. The scope is defined not by which systems are included, but by what the attackers are trying to achieve. This is called an “objective-based” approach.
Key objectives in a red team assessment typically include:
The inclusion of detection evasion as a core objective is one of the defining features of red teaming. It directly evaluates your security operations center (SOC), incident response capabilities, and detection tooling under realistic conditions.
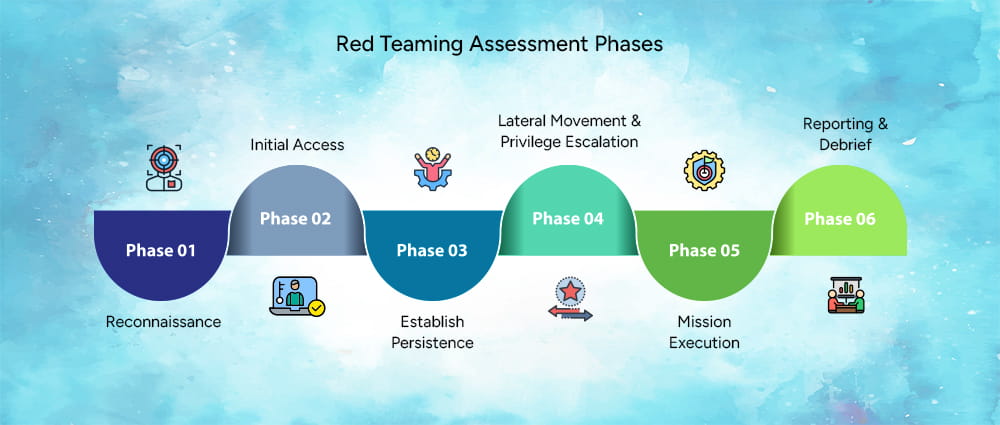
A structured red team assessment methodology typically follows the same kill chain that sophisticated adversaries use in real-world attacks. While specific frameworks vary by provider, most engagements follow these phases:
Phase 1: Reconnaissance. The team conducts extensive open-source intelligence (OSINT) gathering on the target organization. This includes mapping external infrastructure, identifying employees on LinkedIn, reviewing job postings for technology stack clues, and more.
Phase 2: Initial Access. Using intelligence gathered in recon, the team attempts to establish an initial foothold. This could involve targeted spear-phishing campaigns, exploitation of internet-facing vulnerabilities, or physical attempts to access facilities.
Phase 3: Establish Persistence. Once inside, the team deploys mechanisms to maintain access even if the initial vector is discovered and closed.
Phase 4: Lateral Movement & Privilege Escalation. The team moves through the environment, escalating privileges and pivoting toward the defined objectives.
Phase 5: Mission Execution. The team attempts to complete the defined objective, whether that’s data exfiltration, demonstrating access to critical systems, or achieving domain dominance.
Phase 6: Reporting & Debrief. A comprehensive red team assessment report is produced detailing the attack path, detection gaps, and actionable remediation steps.
When you engage a provider for red teaming services, a full-scope engagement typically includes:
Engagements typically run 4 to 12 weeks, with depending on scope, organization size, and objectives.
Continuous penetration testing, commonly called pen testing, is a structured, time-boxed security assessment in which testers are authorized to actively exploit vulnerabilities in a defined scope of systems, networks, or applications. The goal is to identify and validate exploitable weaknesses before real attackers do, and to provide a prioritized, evidence-based remediation plan.
Where red teaming is broad and mission-driven, penetration testing is targeted and vulnerability-driven. It’s designed to give you comprehensive coverage across a defined attack surface, not to simulate the full lifecycle of a sophisticated attack.
Penetration testing services are scoped around systems, not objectives. Common scope types include:
The primary objectives are to identify all exploitable vulnerabilities within scope, demonstrate exploitability with proof-of-concept evidence, understand the potential business impact of each finding, and deliver a prioritized remediation roadmap for your business’s security posture.
Reputable penetration testing service providers don’t wing it. They follow established, industry-recognized methodologies that define what should be tested, how tests should be conducted, and how findings should be reported. The three dominant frameworks in the US market are OWASP, NIST SP 800-115, and PTES.
A standard penetration testing service engagement includes:
Engagements typically run 1 to 4 weeks and cost between $10,000 and $50,000 depending on scope complexity and engagement type.
The Open Web Application Security Project (OWASP) Testing Guide is the gold standard for web application penetration testing. It provides a comprehensive framework of test cases organized around a 12-category structure that covers everything from information gathering and configuration testing to authentication, session management, input validation, and cryptography.
The OWASP Top 10, a regularly updated list of the most critical web application risks, is often used as a baseline for web app penetration test scope. If you’re having a web application tested, verifying that the provider tests against the full OWASP Testing Guide (not just the Top 10) is an important quality indicator.
NIST Special Publication 800-115, “Technical Guide to Information Security Testing and Assessment,” is the federal government’s authoritative guidance on security testing methodology. It’s widely adopted by organizations that need to meet federal compliance requirements, including those operating under FedRAMP, FISMA, or CMMC frameworks.
NIST 800-115 defines a four-phase testing process: planning, discovery, attack, and reporting. It’s particularly valuable for organizations that need defensible, audit-ready documentation of their security testing activities. If your organization does business with the federal government or handles federal data, ensuring your provider follows NIST 800-115 is not optional.
The Penetration Testing Execution Standard (PTES) is a community-driven framework that provides guidance across the full engagement lifecycle, from pre-engagement through reporting. PTES is more technically granular than NIST 800-115 and covers seven sections: pre-engagement interactions, intelligence gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting.
PTES is well-regarded for its depth and is often the baseline for high-quality commercial penetration testing service providers who aren’t bound by federal compliance frameworks.
| Framework | Best For | Scope Focus | Compliance Alignment |
| OWASP | Web applications and APIs | Application layer | PCI DSS, SOC 2 |
| NIST SP 800-115 | Federal / regulated industries | Infrastructure & applications | FISMA, FedRAMP, CMMC |
| PTES | Comprehensive commercial engagements | Full stack | General best practice |
Most mature penetration testing service providers will use elements from multiple frameworks rather than rigidly following just one.
One of the most important decisions in any security assessment is how much information the testing team starts with. This is the “box” paradigm, and it significantly affects what the assessment can tell you.
Before getting into box models, one clarification worth making: white box, black box, and gray box are not separate assessment types. They are simply configuration options that apply to both penetration testing and red teaming, describing how much information the testing team starts with, nothing more.
This distinction matters because vendors often pitch black box penetration tests as being “more realistic” or implicitly closer to red teaming. That framing is misleading. A black box pen test is still a pen test. Understanding the box model helps you see through that and make a more informed scoping decision.
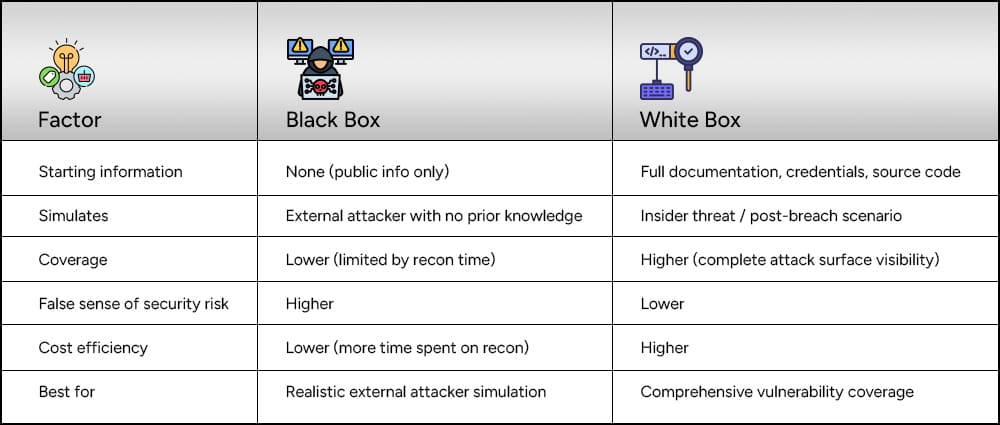
Black box testing is often assumed to be the most “realistic” approach because the testers start with no insider knowledge, just like a real attacker would. That’s partially true, but it comes with a significant drawback: you’re paying experienced testers to spend time doing reconnaissance work that could be minimized or eliminated. You get less vulnerability coverage for the same budget.
White box testing, by contrast, gives testers full visibility into architecture, configurations, and sometimes source code. The result is far more comprehensive coverage of the actual attack surface. For most organizations, white box or gray box testing delivers better ROI.
Gray box testing sits between the two extremes. Testers receive partial information, often a set of credentials, network diagrams, or a high-level architecture overview, simulating a scenario where an attacker has already gained some level of access or knowledge. This is the most commonly recommended approach for network and application testing because it balances realism with efficiency.
Let’s compare the most important things between red teaming and Penetration Testing, and whether they can be used together:
Penetration testing is scoped around systems and is designed to find as many vulnerabilities as possible within that scope. Red teaming is scoped around objectives and is designed to determine whether a defined business-critical outcome can be achieved by a realistic attacker. This is a fundamental philosophical difference, not just a difference in scale.
Penetration testing follows a structured, comprehensive vulnerability discovery methodology (OWASP, NIST, PTES). Red teaming follows an adversary simulation methodology (often based on MITRE ATT&CK) designed to mimic specific threat actor TTPs, including stealth, persistence, and detection evasion.
| Factor | Penetration Testing | Red Teaming |
| Typical duration | 1 to 4 weeks | 4 to 12 weeks |
| Notification of defenders | Usually yes | Usually no (covert) |
| Testing windows | Often business hours | Around the clock |
| Iterative | Rarely | Frequently |
Penetration testing typically costs between $10,000 and $50,000 for a standard engagement. A full red team assessment typically runs $50,000 to $200,000+. The higher cost of red teaming reflects the larger team, longer duration, more sophisticated tooling, and broader operational scope.
Penetration test reports are vulnerability-centric. They list every finding, assign a severity rating, and provide specific remediation guidance for each issue. Red team assessment reporting is narrative-centric. It tells the story of the attack, how the team got in, how they moved, what they accessed, and critically, what detection opportunities were missed along the way.
Penetration testing tells you what holes exist. Red teaming tells you whether those holes, combined with your people and processes, can be combined into a successful attack on something that actually matters to your business. Both perspectives are valuable, but they serve different stakeholder needs.
A quality red team assessment report is one of the most comprehensive documents your security team will ever work with. It should include:
The red team assessment report is not just a list of what went wrong, it’s a strategic roadmap for improving your entire security posture, including the human and process elements that pure technical assessments miss.
A penetration test report is structured differently, centered on findings rather than narrative. Key components include:
Well-executed penetration testing reports allow development and operations teams to immediately begin remediation without needing additional clarification from the testers, a sign of quality that not all providers deliver.
A red team assessment is the right choice when:
Penetration testing is the right choice when:
| Scenario | Recommended |
| Pre-production application launch | Penetration Testing |
| Annual compliance requirement | Penetration Testing |
| Post-breach security validation | Red Teaming |
| SOC and detection maturity testing | Red Teaming |
| Unknown vulnerabilities in defined scope | Penetration Testing |
| Board-level security assurance | Red Teaming |
| Limited budget (under $30k) | Penetration Testing |
| Simulating nation-state or APT threats | Red Teaming |
The most mature security programs don’t treat this as an either/or decision. They use penetration testing to maintain continuous visibility into their technical vulnerability posture and leverage red teaming on an annual or bi-annual basis to validate that their people, processes, and technology controls actually work together when it counts.
Think of it this way: penetration testing keeps your attack surface clean, and red teaming proves that clean attack surface actually translates to real-world resilience. Together, they form a comprehensive security validation program that can withstand scrutiny from regulators, auditors, cyber insurers, and executive leadership alike.
Phase 1: Assessment Planning (Week 1-2)
Start by defining your security objectives and aligning them with business risk. Answer these questions before you do anything else: What are your crown jewel assets? Who are your realistic threat actors? What would a successful attack actually look like? What compliance obligations do you have? With clear answers, you can determine whether penetration testing, red teaming, or both are appropriate, and build a brief red team assessment proposal or PT scope document to share with potential providers.
Key activities in this phase include assembling your internal stakeholders (CISO, IT, Legal), documenting your current security architecture, identifying out-of-scope systems (production databases with live PII, for example), and issuing an RFP or beginning conversations with qualified vendors.
Phase 2: Scope Definition & Methodology Selection (Week 2-3)
Finalize the scope of work with your chosen provider. For penetration testing, this means a detailed list of IP ranges, URLs, applications, and test types. For red teaming, this means defining the objectives, the threat scenario, and the rules of engagement, including what actions are authorized and what constitutes a “flag capture” moment.
Agree on the testing methodology in writing. For pen testing, confirm which frameworks will be followed (OWASP for applications, NIST for infrastructure). For red teaming, confirm the adversary persona and TTPs to be simulated, ideally mapped to MITRE ATT&CK. Get the authorization documents signed. Never start testing without written authorization.
Phase 3: Execution (Week 4-8)
For penetration testing, execution follows a structured sequence: reconnaissance, scanning, vulnerability identification, exploitation, post-exploitation, and documentation. Expect regular communication from your provider with status updates, and have a clear point of contact ready to authorize any activities that fall outside pre-agreed parameters.
For red teaming, execution is less predictable by design. The team will work covertly, and your security operations team will not know the engagement is in progress (this is the “blind” approach). Maintain a small “white cell” of two to three individuals who know the engagement is active, to authorize activities and manage any critical issues that arise. Check in with your provider weekly using a secure channel.
Phase 4: Reporting & Analysis (Week 8-9)
Receive and review the draft report from your provider. For penetration testing, validate that every finding includes the four required elements: description, evidence, business impact, and remediation guidance. For red teaming, validate that the attack narrative is coherent, detection gaps are clearly documented, and all findings are mapped to the MITRE ATT&CK framework.
Schedule a full debrief with your provider. This is not optional. A live walkthrough of findings is significantly more valuable than reading a report in isolation. Ask your team to prepare questions before the debrief, and ensure that both technical and executive stakeholders attend.
Phase 5: Remediation & Follow-Up (Week 10+)
Build a remediation plan with clear owners, timelines, and success metrics for each finding. Prioritize critical and high-severity findings for immediate action, medium findings for the next sprint or quarter, and low findings for the backlog. For red team detection gaps, work with your SOC to build or tune detection rules based on the TTPs documented in the report.
Schedule a retest, ideally with the same provider, to validate that critical and high-severity findings have been effectively remediated. A finding is not closed until it has been retested and confirmed fixed. Build this into your remediation timeline and budget from the beginning.
If there’s one thing to take away from all of this, it’s that red teaming and penetration testing are not competing services, they’re complementary tools for different security maturity levels and different questions. Use the wrong one at the wrong time, and you’ll either waste money or walk away with a false sense of security. Use the right one, and you get something genuinely valuable: evidence-based confidence in your security posture.
Here’s a quick summary to guide your decision:
Your next step is straightforward: have an honest internal conversation about where you are in your security maturity journey. If you’re not sure what vulnerabilities exist in your environment, start with a penetration test. If you’ve been patching and hardening and you want to know whether all that work actually translates to real-world resilience, it’s time to bring in a red team.
That’s where Arpatech’s security team comes in. Whether you need a scoped penetration test, a full red team engagement, or a structured Governance, Risk and Compliance (GRC) program to tie your security controls to business risk, Arpatech has the expertise to guide you from assessment through remediation.
The GRC and cybersecurity practices in particular helps organizations build the policy frameworks, risk registers, and compliance roadmaps that make security assessments more meaningful, because knowing what’s broken is only useful if you have the governance structure to fix it systematically and keep it fixed.
Either way, the worst decision you can make is no decision at all. The adversaries targeting your organization aren’t waiting for your budget cycle to close. Arpatech’s team is ready to help you figure out exactly where to start.
Penetration testing focuses on finding and exploiting specific technical vulnerabilities in a defined scope. Red teaming simulates a real attacker over a longer period, combining technical, physical, and social tactics to test how well your people, processes, and detection capabilities respond.
A red team operates like an advanced threat actor. They use stealth, phishing, privilege escalation, lateral movement, and persistence techniques to reach predefined objectives without being detected, while the blue team attempts to detect and respond in real time.
Clarify your objectives, scope, critical assets, rules of engagement, internal readiness, and whether your detection and response teams will be informed or tested blindly.
Red teaming is an adversary simulation exercise that mimics real-world cyberattacks to evaluate an organization’s overall security posture, including detection, response, and resilience.
White box testing gives testers full knowledge of the system, such as architecture and credentials. Black box testing provides no internal information, simulating how an external attacker would approach the target.
Penetration tests are typically lower cost due to shorter duration and limited scope. Red team assessments cost more because they run longer, require broader expertise, and test multiple layers of security beyond just technical flaws.