In today’s digital landscape, cyber threats are evolving at an unprecedented pace. Among these, zero-day vulnerabilities are some of the most dangerous. They exploit weaknesses in software that developers are unaware of, leaving organizations exposed to attacks that can have severe consequences.
This blog will guide you through the world of zero-day vulnerabilities, from discovery to defense, and how enterprises can stay protected.
When you hear the term “zero-day,” it might sound like tech jargon, but it is a concept every organization should understand.
A zero-day vulnerability refers to a flaw in software that is unknown to the software vendor or developer. The “zero-day” part comes from the fact that developers have had zero days to fix the vulnerability. In other words, attackers can exploit it before a patch or fix is available.
These vulnerabilities are highly prized by hackers because they enable attacks to go undetected. Once the software maker discovers a patch, it is developed, but until then, your systems remain exposed.
For those keeping up with cyber incidents, you may have seen headlines like zero-day vulnerability news or zero-day vulnerability today, highlighting the immediacy and risk of these threats.
Understanding how zero-day attacks work is essential to defending against them.
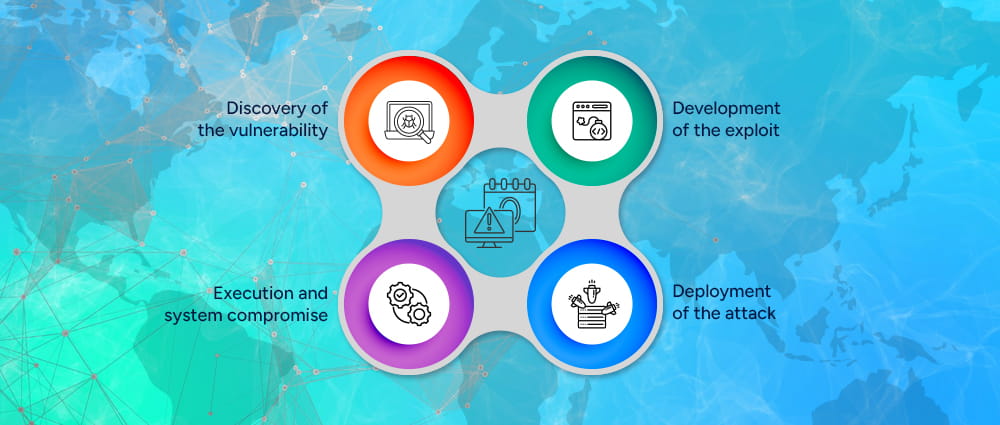
Attackers take advantage of the unknown flaw in software to execute malicious actions. This could range from stealing sensitive data to taking over entire networks. A typical zero-day attack follows these stages:
The first step in a zero-day vulnerability attack is discovering the flaw. Hackers or security researchers identify a weakness in software, hardware, or an operating system that has not yet been discovered by the vendor.
Cybercriminals often use advanced techniques such as fuzz testing, reverse engineering, and automated vulnerability scanning to locate these weaknesses. In some cases, attackers discover the flaw before anyone else and quietly develop tools to exploit it.
Sometimes the discovery is accidental. In other cases, highly skilled attackers deliberately search for vulnerabilities in widely used platforms like web browsers, operating systems, or enterprise software. Once the flaw is identified, it becomes extremely valuable because there is no patch or defense available yet.
This stage is why zero-day vulnerability news often creates urgency in the cybersecurity community. The moment the vulnerability becomes public knowledge, organizations rush to assess whether their systems are exposed.
Once attackers discover the vulnerability, the next step is to create an exploit that takes advantage of it. This is where the 0-day exploit or zero-day exploit is developed.
An exploit is essentially a piece of code designed to trigger the vulnerability and allow attackers to perform malicious actions. These actions might include installing malware, escalating privileges, bypassing authentication systems, or gaining administrative control over a network.
Developing a reliable exploit often requires extensive testing. Attackers need to ensure that the exploit works consistently across different versions of the targeted software. In some underground cybercrime markets, fully developed zero-day exploits can be sold for thousands or even millions of dollars because they can compromise thousands of systems before a patch is released.
During this stage, attackers also work on making the exploit stealthy so it can avoid detection by traditional antivirus or security monitoring systems.
After building the exploit, attackers need a way to deliver it to their target. This stage involves distributing the exploit through different attack vectors.
Common deployment methods include:
A zero click exploit is particularly dangerous because it can compromise a device without the victim clicking anything or opening any files. Some attacks simply require a message to be received on a device or a background service to process malicious data.
Once deployed, the exploit quietly enters the target system and prepares to execute the malicious code.
The final stage of a zero-day attack is execution. At this point, the exploit successfully triggers the vulnerability and allows the attacker to gain unauthorized access to the system.
Depending on the attacker’s goal, this stage may involve:
In many cases, attackers remain undetected for weeks or even months. Because the vulnerability was previously unknown, traditional security tools may not immediately recognize the malicious activity.
This is why zero day attack prevention requires a proactive security strategy that includes behavioral monitoring, threat intelligence, and continuous system analysis.
Not all hackers are created equal. Understanding who might carry out a zero-day attack helps in anticipating and preparing defenses.
Some common perpetrators include:
Recognizing the source can guide your enterprise in deploying the right zero day protection measures and monitoring systems for suspicious activity.

While any system can theoretically be affected, certain systems are more frequently targeted:
Organizations running outdated software, unpatched systems, or lacking robust monitoring are more susceptible. Keeping systems up-to-date is crucial, but even that may not be enough against newly discovered zero-day attacks.
Spotting a zero-day attack is challenging since there is no signature in known malware databases. However, enterprises can take proactive steps:
Security teams should continuously monitor systems for unusual network activity or irregular user behavior. This may include unexpected login attempts, sudden spikes in data transfers, or users accessing systems outside their normal roles. Behavioral monitoring tools help detect patterns that may indicate a hidden zero day exploit operating within the network.
Advanced EDR solutions provide visibility into activity across laptops, servers, and other endpoints. These tools analyze processes, file changes, and system behavior to identify anomalies that traditional antivirus software might miss. By detecting suspicious actions early, EDR tools can help stop potential attacks before they spread across the organization.
Threat intelligence platforms provide real-time updates on emerging cyber threats and vulnerabilities. By following reliable zero-day vulnerability news and alerts about zero-day patched today, security teams can respond quickly when new risks appear. This allows organizations to apply temporary defenses or security controls while waiting for official patches.
Regular security audits, penetration testing, and vulnerability assessments help organizations identify weaknesses in their infrastructure. These tests simulate real-world attacks to reveal gaps in security controls before hackers can exploit them. Conducting audits frequently ensures that systems remain resilient against both known and emerging threats.
Employees are often the first line of defense against cyber threats. Training staff to recognize phishing emails, suspicious attachments, and unusual system behavior can help prevent attacks from spreading. When employees understand how zero-day exploits may be delivered, they are more likely to report suspicious activity quickly.
Combining these strategies helps create a multi-layered defense, making it harder for attackers to succeed.

Learning from past incidents can highlight the dangers of unpatched vulnerabilities. Some notable exploit examples include:
In early 2021, hackers exploited previously unknown vulnerabilities in Microsoft Exchange Server, a widely used enterprise email system. These zero-day vulnerabilities allowed attackers to access corporate email accounts, steal sensitive information, and even install backdoors for future access.
The scale of the attack was massive, affecting tens of thousands of organizations globally. Many companies were caught off guard because the vulnerabilities had not been publicly disclosed, and no patch was available initially.
The incident emphasized the need for enterprises to monitor zero-day vulnerability news closely and apply emergency patches as soon as they become available to prevent widespread compromise.
In 2022, researchers discovered an iOS vulnerability that allowed attackers to take over iPhones silently. The exploit could be delivered via messages or background processes without the user’s knowledge.
Once executed, the attacker could access sensitive data, including contacts, messages, and location. This example shows how sophisticated zero-day attacks can bypass traditional defenses and underscores the importance of layered security measures, such as endpoint monitoring and behavioral analysis, to detect unusual activity.
The SolarWinds incident is one of the most high-profile cyberattacks in recent US history and also involved zero-day vulnerabilities. Hackers compromised the Orion software updates from SolarWinds, a popular IT management platform used by thousands of companies and government agencies.
By injecting malicious code into a trusted software update, the attackers created a 0-day exploit that gave them access to corporate networks without triggering any warnings. This allowed them to move laterally across systems, steal sensitive data, and monitor communications for months before being detected.
The SolarWinds attack highlighted how even trusted software providers can become a vector for zero-day attacks, making supply chain security and proactive monitoring essential for all enterprises.
These examples underline the importance of timely zero-day protection and continuous monitoring to prevent similar breaches in enterprises today.
While no security measure is foolproof, using multiple layers of security can greatly reduce risk. Since zero day exploits target unknown vulnerabilities, organizations must focus on prevention, monitoring, and quick response. Here are five practical steps enterprises can take to strengthen their zero-day vulnerability protection strategy.
Keeping software updated is one of the simplest yet most effective security practices. Organizations should regularly scan their systems to identify outdated software, weak configurations, or missing security updates. Even though a zero-day vulnerability may not have a patch immediately, many attacks still succeed because companies delay routine updates.
When vendors release updates or announce a zero-day patched today, security teams should apply those patches quickly. Automating patch management and maintaining an inventory of all software systems can help reduce the chances of attackers exploiting known weaknesses.
Traditional antivirus software often struggles to detect new 0-day exploits. That is why modern security tools focus on behavioral analysis instead of only relying on known malware signatures. These tools look for unusual activity within systems, which can help identify threats early.
Enterprises should also follow trusted cybersecurity sources and threat intelligence feeds. Staying updated with zero-day vulnerability news allows organizations to respond quickly if a zero-day vulnerability today affects commonly used software.
Network segmentation helps limit the damage if an attack occurs. Instead of keeping all systems connected in one large network, organizations divide them into smaller sections. If attackers gain access to one part of the network through a zero day exploit, segmentation can stop them from moving further.
At the same time, companies should apply the principle of least privilege. This means employees and systems only get the access they truly need. Limiting permissions reduces the chances of a small breach turning into a large-scale attack.
Since zero-day attacks are difficult to detect, monitoring system behavior becomes very important. Security tools such as SIEM and XDR help track activity across networks, servers, and user accounts in real time.
These platforms look for unusual patterns, such as unexpected login attempts, strange network traffic, or unauthorized access requests. Detecting these signs early can help security teams stop zero day attacks before they cause serious damage.
A strong backup and recovery plan ensures that businesses can continue operating even if an attack succeeds. Companies should regularly back up important data and store it in secure locations that attackers cannot easily access.
This strategy is especially useful during ransomware attacks caused by a zero day exploit. If systems are compromised, organizations can restore their data and resume operations quickly without major losses.
Following these tips can significantly strengthen your organization’s zero day prevention strategy and reduce exposure to unknown cyber threats.
Zero-day vulnerabilities represent one of the most serious threats in today’s cybersecurity landscape. From understanding what day zero is to implementing advanced defense strategies, proactive measures are key. While tools and monitoring are essential, partnering with experts can provide the guidance your enterprise needs.
At Arpatech, our team specializes in zero-day protection and cybersecurity consulting. We help organizations identify potential threats, implement prevention measures, and maintain a strong defense posture. With our expertise, enterprises can move towards a world with no zero days, ensuring operational continuity and safeguarding sensitive data against emerging threats.
No, zero-day vulnerabilities cannot be fully prevented because they exploit unknown software flaws. However, enterprises can significantly reduce risk with zero-day protection strategies such as proactive monitoring, layered defenses, regular system audits, and rapid patch deployment once vulnerabilities are discovered.
Detection of a zero-day attack can take days, weeks, or even months because traditional security tools rely on known malware signatures.
Using advanced tools like endpoint detection and response (EDR), behavioral monitoring, and threat intelligence can shorten detection time and help identify 0-day exploits before they cause major damage.
Traditional patch management addresses known vulnerabilities after vendors release a fix. In contrast, zero-day vulnerability protection focuses on preventing attacks from unknown vulnerabilities or zero-day exploits before patches exist.
It relies on behavioral monitoring, threat intelligence, and multi-layered security rather than just waiting for updates.
Organizations should prioritize protecting critical systems, sensitive data, and externally exposed endpoints.
Investments in zero-day attack prevention should include advanced threat detection tools, behavioral monitoring, employee cybersecurity training, and partnerships with experts who can guide in handling zero-day exploits effectively.
Threat intelligence is highly important for zero-day protection because it provides real-time alerts on emerging vulnerabilities, zero-day vulnerability news, and available patches.
By using this information, companies can respond quickly to threats, implement temporary mitigations, and reduce the risk of successful zero-day attacks.