If the past few years have taught security leaders anything, it’s this: your organization is only as secure as your weakest vendor.
From cloud providers and SaaS tools to payment processors and logistics partners, modern businesses rely heavily on third parties. This interconnected ecosystem creates speed and innovation, but it also expands your attack surface in ways that are hard to control.
That’s where Third Party Risk Management (TPRM) comes in.
It was reported that breaches involving third-party vendors and supply chain partners cost financial organizations an average of $4.91 million per incident, ranking as the second most costly type of breach after insider attacks.
This is why in 2026, TPRM is no longer just a compliance checkbox. It is a strategic function that directly impacts business resilience, customer trust, and revenue continuity. For CISOs, the challenge is not just managing vendors but building a scalable, intelligent system that can keep up with evolving cyber threats.
This guide breaks down everything you need to know, from foundational concepts to advanced strategies, in a clear and practical way.
When it comes to Third-party risk management, it is the process of identifying, assessing, and mitigating risks that arise from working with external vendors, suppliers, or partners.
These risks include:
In 2026, the threat landscape has shifted dramatically:
A single compromised vendor can expose millions of records or disrupt entire operations. That’s why third party cyber risk management is now a board-level concern.
Investing in third party vendor risk management is not just about avoiding breaches. It has a direct business impact.
A proactive third party cyber risk management approach helps organizations identify vulnerabilities before they are exploited. Instead of reacting to incidents, businesses can take preventive measures such as enforcing stronger controls or limiting vendor access.
Over time, this significantly reduces the likelihood of costly and damaging breaches.
When vendors are properly assessed and monitored, organizations are better prepared to handle disruptions.
This includes having backup vendors, clear escalation processes, and defined recovery plans. As a result, businesses can maintain continuity even when unexpected issues arise.
Customers today are more aware of how their data is handled, and they expect organizations to ensure security across the entire supply chain. Demonstrating strong third party risk management practices reassures customers that their data is protected, even when handled by external providers.
A structured TPRM program ensures that vendor-related risks are documented, assessed, and monitored in line with regulatory requirements.
This not only decreases the risk of fines but also simplifies audits and reporting processes.
With proper risk scoring and vendor insights, organizations can make more informed decisions about what vendors to onboard, retain, or replace. This shifts vendor management from guesswork to a data-driven strategy.
Organizations that neglect TPRM often face:
In short, why is third party risk management important? Because
it protects both your bottom line and your brand.
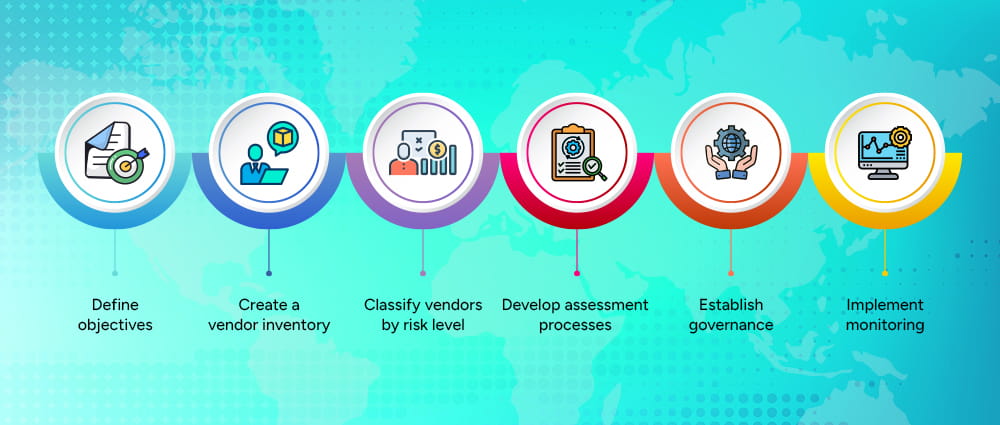
Creating an effective third party risk management framework requires structure, clarity, and executive buy-in.
The first step in building an effective TPRM program is to clearly identify what success looks like. This includes aligning the program with broader business goals such as risk reduction, compliance, and operational efficiency. When you don’t have clear objectives, it becomes difficult to measure effectiveness or gain executive support.
A common problem in many organizations is not knowing exactly how many vendors they work with or what access those vendors actually have. Building a single, centralized list of all third parties brings much-needed clarity.
This list should include everyone, from major service providers to subcontractors and even tools adopted without formal approval. Having this visibility makes it much easier to understand your exposure and manage vendor-related risks with confidence.
Every vendor does not carry the same weight when it comes to risk. A cloud provider storing customer data is naturally more critical than a design agency handling marketing materials.
By grouping vendors into risk categories, teams can focus their time and resources on the relationships that matter most, instead of treating all vendors the same.
Without a clear process, vendor assessments can become inconsistent and subjective. Defining a standard way to evaluate vendors helps ensure fairness and accuracy.
This means deciding what questions to ask, what proof to request, and how to measure risk in a repeatable way. A structured method removes guesswork and leads to more reliable outcomes.
A TPRM program works best when everyone knows their role. Governance outlines who is responsible for assessments, who makes decisions, and how issues are escalated.
When responsibilities are clearly defined, the program runs more smoothly and avoids confusion or delays.
Vendor risk changes over time as systems, threats, and business relationships evolve. Ongoing monitoring helps organizations stay aware of any shifts in a vendor’s security posture or compliance status.
This allows teams to respond to new risks early, rather than being caught off guard after an incident occurs.
A successful program requires cross-functional collaboration.
To build a strong TPRM program, organizations rely on established frameworks.
The NIST CSF provides a flexible and widely adopted approach to managing cybersecurity risks, including those related to third parties. It helps organizations protect, identify, detect, respond to, and recover from risks in a structured way.
This framework focuses specifically on supply chain risk management. It provides detailed direction on how to identify and mitigate risks associated with vendors and suppliers, making it highly relevant for TPRM programs.
These international standards define best practices for information security management and supplier relationships. Organizations that align with ISO standards demonstrate a strong commitment to security and risk management.
SOC 2 reports provide assurance that a vendor has implemented appropriate controls for security, availability, and confidentiality. Reviewing these reports is a key part of vendor due diligence.
Using a recognized third party risk management framework ensures consistency and audit readiness.
A complete third party risk management process includes several critical stages.
Each stage plays a role in minimizing exposure.
Manual TPRM processes are no longer sustainable. Organizations now rely on third party risk management software to scale their efforts.
Risk scoring allows organizations to quantify vendor risk based on predefined criteria. This makes it easier to compare vendors and prioritize mitigation efforts, especially when dealing with a large number of third parties.
Manual questionnaires can be time-consuming and inconsistent. Automation streamlines the process, ensuring faster responses and more accurate data collection from vendors.
Continuous monitoring tools provide real-time insights into vendor risk posture. This includes detecting vulnerabilities, breaches, or compliance issues as they occur.
A good third party risk management platform should integrate seamlessly with existing systems such as SIEM, GRC, and procurement tools. This ensures a unified approach to risk management.
Clear and customizable dashboards help stakeholders understand vendor risk at a glance. This is particularly important for executive reporting and decision-making.
In 2026, third-party risk management software is essential for efficiency and scalability.

To stay ahead of threats, organizations should follow proven best practices.
Instead of spreading resources thin across all vendors, organizations should focus on those that pose the highest risk. This ensures that critical vulnerabilities like zero day attack are addressed first, improving overall security effectiveness.
Consistency is key to reliable risk management. Standardized processes ensure that all vendors are evaluated using the same criteria, reducing variability and improving accuracy.
Risk-based models allow organizations to allocate resources more efficiently by focusing on vendors with the highest potential impact.
Automation reduces manual effort and allows teams to focus on strategic activities such as risk analysis and decision-making.
Regular audits ensure that vendors continue to meet security and compliance requirements over time.
Educating employees about vendor risks and TPRM processes improves overall program effectiveness and reduces human error.
Strong execution is what separates mature TPRM programs from basic ones.
Compliance is a major driver of TPRM adoption in the US.
Third party risk management compliance ensures organizations meet legal requirements while reducing risk.
Vendor risk identification is the foundation of third party cyber risk management.
Understanding how vendors access, store, and protect data is critical. This includes evaluating encryption methods, access controls, and data retention policies.
Vendors should have strong network security measures in place, including firewalls, intrusion detection systems, and secure configurations.
A vendor’s ability to respond to incidents can significantly impact the outcome of a breach. Organizations should assess whether vendors have documented and tested response plans.
Did you know that human error has remained one of the leading causes of security incidents. Vendors should provide regular training to their employees to reduce this risk.
Vendors often rely on their own suppliers, creating additional layers of risk. Understanding these dependencies is essential for comprehensive patch management and risk management.
Assign scores based on:
This helps prioritize mitigation efforts.
A strong TPRM program supports broader information security risk management goals.
Organizations that integrate TPRM into their overall risk strategy gain a competitive advantage.
Conducting a structured risk assessment is critical for any effective Third Party Risk Management program. It helps organizations move from assumptions to data-driven decisions by clearly identifying where risks exist, how severe they are, and what actions need to be taken.
The step-by-step process is:
The first step is to clearly define what you are trying to protect. This includes not just obvious assets like databases and applications, but also less visible ones such as APIs, cloud workloads, intellectual property, and customer data handled by vendors. In a third-party context, you also need to map which vendors have access to which assets.
For example, a SaaS provider may have access to customer records, while a logistics vendor may interact with operational systems. Creating a detailed asset inventory ensures that nothing critical is overlooked and provides a strong foundation for the rest of the assessment.
Once assets are identified, the next step is to understand what could potentially harm them. Threats can range from external cyberattacks such as ransomware and phishing to insider threats, system failures, or even natural disasters affecting vendor operations.
In third-party environments, it is especially important to consider supply chain attacks, where attackers exploit vulnerabilities in vendors to gain access to your systems. Thinking in terms of real-world attack scenarios, rather than abstract risks, makes this step far more practical and actionable.
After identifying threats, you need to evaluate where your defenses may be weak. Vulnerabilities can exist in vendor systems, processes, or even human behavior.
This includes outdated software, misconfigured cloud settings, weak access controls, or lack of employee training. Reviewing vendor security questionnaires, audit reports, and technical assessments can help uncover these gaps.
The goal here is to understand not just whether a vulnerability exists, but how easily it could be exploited in a real-world scenario.
Not all risks are equal, which is why understanding the potential impact is crucial. This step involves analyzing what would happen if a threat successfully exploited a vulnerability. Would it result in data loss, regulatory penalties, operational downtime, or reputational damage?
For example, a breach involving customer data may have severe legal and financial consequences, while a minor system outage may have limited impact. By clearly defining the potential outcomes, organizations can prioritize risks based on business impact rather than just technical severity.
Risk is typically calculated by combining the likelihood of a threat occurring with the impact it would have. This step transforms qualitative observations into measurable risk levels, often categorized as low, medium, or high. Some organizations use scoring models or risk matrices to standardize this process.
For instance, a highly likely threat with severe impact would be classified as high risk and require immediate attention. This structured approach helps ensure consistency across assessments and supports better decision-making.
The final step is to take action by applying appropriate mitigation strategies. Controls can include technical measures like encryption and multi-factor authentication, administrative actions such as updated policies and vendor training, or contractual requirements that enforce security standards.
In some cases, organizations may decide to reduce risk by limiting vendor access or even replacing high-risk vendors altogether. The key is to ensure that controls are practical, measurable, and aligned with the level of risk identified. Risk assessment is not complete until it leads to tangible improvements in security posture.
Tools used
Consistency is key to accurate results.
TPRM is not just for large enterprises. Here are the challenges that small businesses face.
Even a basic program can significantly reduce risk.
The next evolution of TPRM is driven by AI third party risk management.
AI is not replacing humans, but it is making TPRM smarter and more proactive.
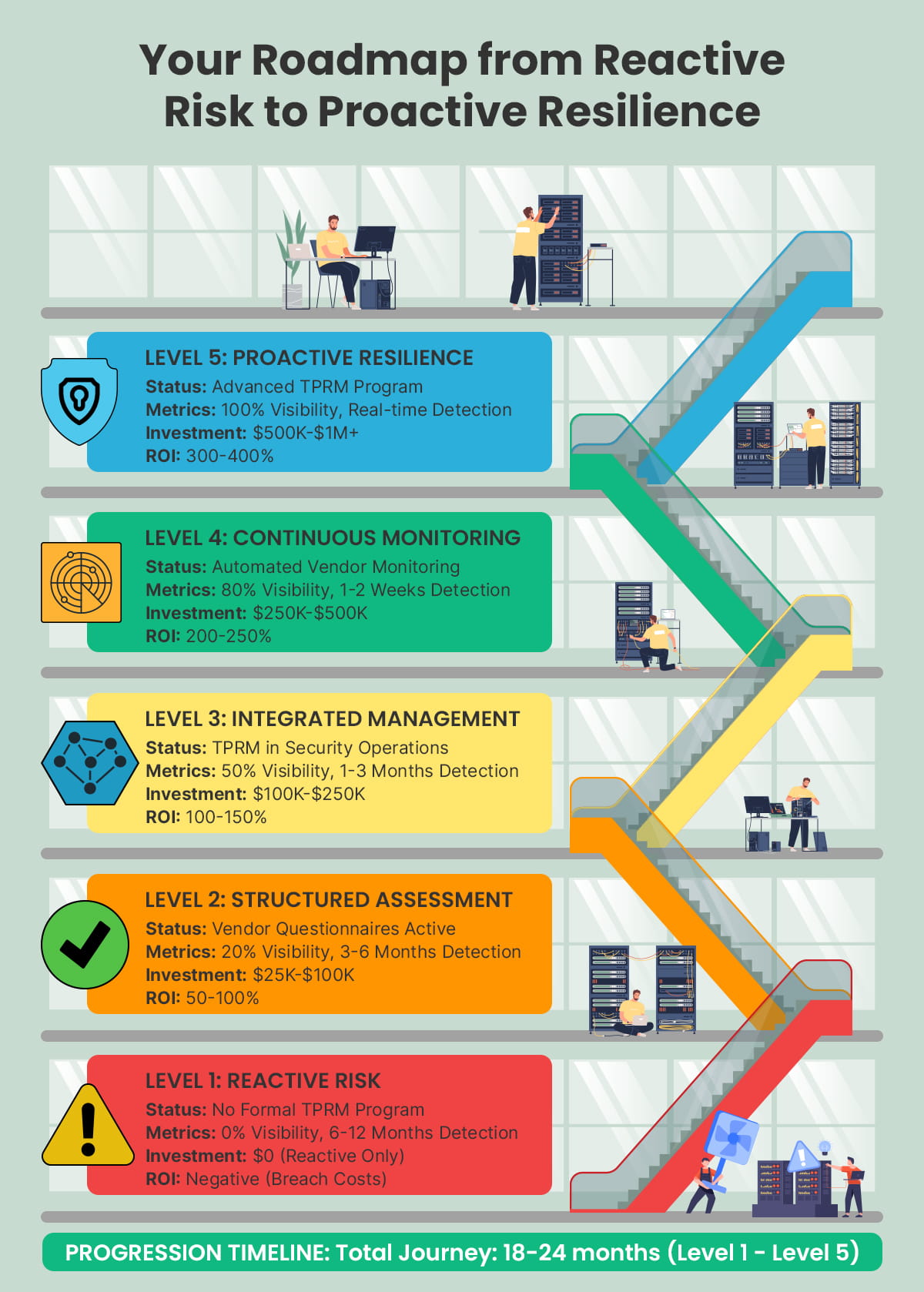
The practice of Third Party Risk Management became essential for modern cybersecurity operations in 2026.
Organizations that treat TPRM as a strategic capability, and not just as a compliance requirement, are better positioned to prevent any breaches in their system, maintain operational resilience at all hours, build customer trust, and achieve long-term growth without any hitch in the process.
CISOs have established guiding principles for their professional development. The Arpatech structured program development requires organizations to adopt technological solutions while using AI for ongoing improvements.
Because in today’s interconnected world, securing your organization means securing your entire ecosystem.
Vendor Management focuses on the business relationship with suppliers. It deals with contracts, pricing, performance, service delivery, and overall collaboration. The goal is to ensure vendors deliver value to the organization.
Third Party Risk Management (TPRM), on the other hand, focuses specifically on identifying, assessing, and reducing the risks that vendors introduce. This includes cybersecurity risks, data protection concerns, and compliance issues.
In simple terms, vendor management asks, “Is this vendor doing their job well?”
Third party vendor risk management asks, “Is this vendor exposing us to risk?”
Both functions work together, but third party risk management is centered on security, risk, and compliance rather than performance and cost.
Third party risk management compliance is a major reason organizations invest in TPRM programs. US regulations such as HIPAA, GLBA, CCPA, and SEC cybersecurity rules require organizations to ensure that their vendors also follow proper security and data protection practices.
A strong third party risk management framework helps organizations:
By implementing effective third party cyber risk management, organizations can prove to regulators that they are actively managing vendor-related risks and protecting customer data across the supply chain.
AI third party risk management is transforming how organizations handle vendor risk. Traditional TPRM processes are manual, time-consuming, and difficult to scale as the number of vendors grows.
AI improves third party risk management by:
With AI-powered third party risk management tools, CISOs can focus less on paperwork and more on strategic risk decisions, making TPRM faster, smarter, and more proactive.